 |
|
| Mobile-sized | ||
| This site: | ||
| Home | ||
| Copyright | ||
| Let the Devil Wear Black: | ||
| Briefly. | ||
| ||
| Additional Resources... | ||
| James Linden: | ||
| Background | ||
| Contact | ||
Resources - Chain of evidence
Links from a broken chain - it only takes one.
Chapter 14
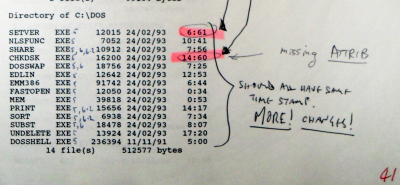
We learned from statements made under oath by the company that with permission from David Snaith (the dismissing officer), Col Burgess (the IT man) had gone in, before the computer data-copying for the InComp computer report took place and changed the hidden status of directories and files, thus breaking the chain of evidence.
Let me just say that again: the dismissing officer knew at the time of the dismissal that the key evidence was corrupted at his own instruction.
Doing so was presented at the tribunal as the explanation as to why InComp could not find any hidden directories and so on.
Here, we can see that the hidden status wasn't the only thing that was changed.
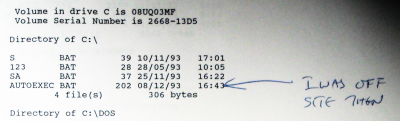
Of course, this wasn't the only example of breaking the chain of evidence and an unquestionable example is here, where the autoexec.bat file has been changed for some reason after I had left the site.
Breaking the chain of evidence renders as useless anything that can be claimed from that evidence by the company and anything derived from that - and so on.
It is like poisoning the root of a tree - the whole tree dies.
All of the case that had any part of it derived directly or indirectly from this report was of no worth in a case against me.
Although, it was potentially of great value in a case of corruption against the company - something that Snaith, with his resistance to producing evidence, demonstrated he knew of right from the beginning.
This was all getting very ‘Edge of Darkness’ again.